An AI agent can do more than just answer requests.
It can:
- Change data
- Send API requests
- Create files
- Or run processes
That means it can perform actions in the real world.
And this is exactly where a new problem appears.
Because not all actions are safe.
An agent can:
- Delete data
- Spend money
- Or make a request to an external system
Even if you did not plan that.
So an agent must not be allowed to do everything.
It needs boundaries.
What allowed actions are (Permissions)
An agent does not have direct access to tools.
It cannot on its own:
- Open a file
- Change a database record
- Or send an API request
To perform an action, it has to use a tool.
And only the tools it is allowed to call.
This list of allowed actions is exactly its Permissions.
They define:
- What the agent can do
- And what it cannot
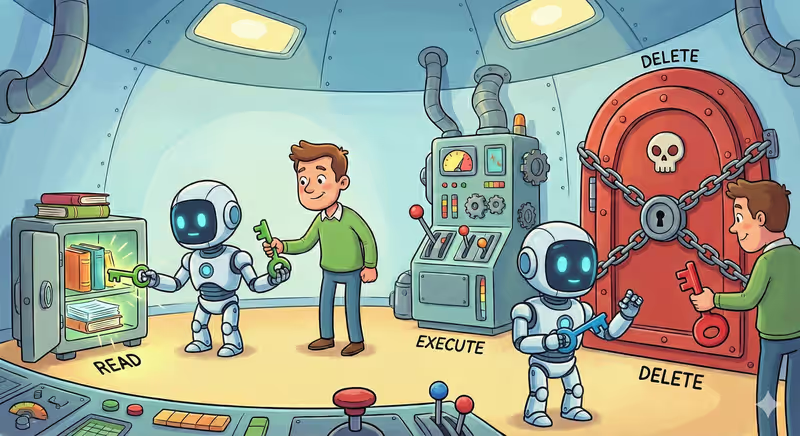
Permission levels
Not all actions are equally safe.
That is why permissions are usually split into levels, depending on how strongly the agent can affect the system.
Read
The agent can retrieve data. But it cannot change it.
For example: read a database row, open a file, check status.
Write
The agent can create or modify data.
For example: create a new record, update a file, save a result.
Execute
The agent can call processes or external services.
For example: send an API request, run a script, call a webhook.
Delete
The agent can delete data or records.
This is the most dangerous level.
Because the action is irreversible.
The higher the permission level, the more the agent can change in the world.
So it gets only the access required to complete the task.
Why an agent must not get access to everything
An agent does not understand consequences of its actions.
It picks the tool that looks most suitable in the current context.
| Level | What is allowed | Risk |
|---|---|---|
| Read | Retrieve data | Low |
| Write | Create or modify | Medium |
| Execute | Run processes or API | High |
| Delete | Delete data | Critical |
But "suitable" does not always mean "safe".
An agent can:
- Write wrong data
- Call a paid API
- Or delete an important file
Simply because that helps complete the task.
If you give it access to everything, it can do more than you expected.
Who sets the boundaries
An agent does not choose its permissions by itself.
It does not decide:
- Which tools it can access
- Which actions it can perform
These boundaries are set by a human.
Or by a system that defines:
- Which tools are allowed
- Which actions can be performed
- And at which access level
The agent only works within these rules.
Principle of least privilege
There is a simple rule:
An agent gets only the access required to complete a specific task.
No more.
This is called the principle of least privilege.
If an agent only needs read access, it must not get write access.
If it needs to create a file, it must not be able to delete it.
Fewer permissions means fewer risks.
In code this looks like
Below is the same principle in a simple format:
we explicitly define what the agent is allowed to do, and force the system to check this before every action.
1) We have tools with different risk levels
def read_user(user_id: int):
return {"id": user_id, "status": "active"}
def update_user(user_id: int, status: str):
return {"id": user_id, "status": status}
def send_webhook(event: str):
return {"sent": event}
def delete_user(user_id: int):
return {"deleted": user_id}
TOOLS = {
"read_user": {"level": "read", "handler": read_user},
"update_user": {"level": "write", "handler": update_user},
"send_webhook": {"level": "execute", "handler": send_webhook},
"delete_user": {"level": "delete", "handler": delete_user},
}
2) Here we define permissions for this specific agent
AGENT_PERMISSIONS = {"read", "write"} # execute and delete are forbidden
3) The model asks to perform an action
model_output = {
"action": "update_user",
"parameters": {"user_id": 42, "status": "paused"},
}
4) The system checks permissions before execution
def run_action(call: dict):
action = call["action"]
params = call["parameters"]
tool = TOOLS.get(action)
if tool is None:
return {"error": "Tool not found"}
if tool["level"] not in AGENT_PERMISSIONS:
return {"error": "Action not allowed"}
return tool["handler"](**params)
5) If the level is allowed, we run the action
result = run_action(model_output)
# {"id": 42, "status": "paused"}
If the model requests delete_user, the system returns:
{
"error": "Action not allowed"
}
Full implementation example with connected LLM
Analogy from everyday life
Imagine you give someone keys to your apartment.
If they only need to water flowers, you give them the door key.
But you do not give:
- The safe key
- Access to your banking app
- Or your card PIN code
Because more access means more can be changed.
Even by accident.
That is why you give only the keys needed for the specific task.
In short
An agent can perform actions through tools.
But it is allowed:
- Only specific tools
- Only specific action types
- And only at a specific access level
Usually, the principle of least privilege is used:
The agent gets only the access needed to complete the task.
FAQ
Q: Can an agent perform any action through tools?
A: No. It can use only the tools and actions it is allowed to use.
Q: Who defines what an agent is allowed to do?
A: A human or a system that sets the list of available tools and their access level.
Q: What is the principle of least privilege?
A: It is a rule where the agent gets only the access needed for a specific task.
What’s next
Now you know what an agent is allowed to do.
But even with restrictions, it can:
- Get stuck in a loop
- Repeat the same actions
- Or spend resources
So sometimes an agent has to stop on its own.
Or be stopped by the system.